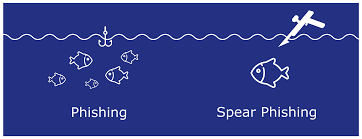
Phishing in a 100 words or less. From Crowd Strike:
Spear Phishing:
“Spear-phishing is a type of phishing attack that targets specific individuals or organizations typically through malicious emails. The goal of spear phishing is to steal sensitive information such as login credentials or infect the targets’ device with malware.
Spear phishers carefully research their targets, so the attack appears to be from trusted senders in the targets’ life. A spear phishing email uses social engineering techniques to urge the victim to click on a malicious link or attachment. Once the victim completes the intended action, the attacker can steal the credentials of a targeted legitimate user and enter a network undetected. “
Phishing:
“Phishing attacks prioritize quantity. The messaging in phishing emails, texts or phone calls are generic and sent to a large group of individuals or organizations in hopes of increasing the chance of “catching” a victim. Phishing attacks via phone calls are often called vishing for voice-phishing. Attacks via text messages are known as smishing for SMS-phishing.”
Whaling:
“A whaling attack prioritizes C-level targets. Whaling uses the same personalized strategy of spear-phishing attacks, except attackers specifically target higher level management to expose financial and confidential information. Whaling attacks hope to extract more valuable, classified information by taking down big targets, which can magnify the damage inflicted upon an organization.”
Bottom line is that Phishing, Spear-Phishing, and Whaling are very similar to marketing. The targets are one or more folks. Individuals are categorized into 1..N groups. The groups are based upon similar characteristics. Things like interest in sports, fashion, buying power,etc. Phishing types of campaigns go deeper by identifying position in a company, debt, maturity, relationships, names of kids, marital status, self worth, etc. Marketing campaigns try to influence you to buy something. Phishing types of campaigns try to assume your identity, and compromise your computer, your network – connection to other computers and your relationships, etc.
Phishing campaigns are extremely successful. The deck is stacked in favor of phishing campaigns to be successful. If you are going to bet on anything, bet on the attacker that leverages a phishing type of attack. Much better than the odds in Vegas.

There are a number of reasons why the odds favor the phishing attacker.
From the book “The Weakest Link“:
Information Advantage:
When you go to Vegas, unless you are a “high roller” or someone they know that has tried to scam them before, the folks in Vegas don’t know that much about the average Joe/Jane that comes in off the street to play the slots – they know how to separate you from your money, but the technique is not based upon a unique individual. However, what is known to the data collectors around the world such as Google, Amazon, Facebook, Twitter, Zhenhua, etc. is detailed information about each individual on social media. Data collectors can tell you what you will mostly eat for breakfast, where you shop for golf clubs, what car you drove ten years ago, what you paid for the car, the amount you got for selling your car, when you are on vacation,etc. Attackers initiating phishing types of attacks leverage this information to zero in on targets giving them an enormous advantage over the intended target. Another positive for the attacker is that the target provides the information without any questioning. Plus one for the attacker. Zero for the individual.
Knowledge Advantage:
You don’t have to be a highly trained programmer to launch a cyber attack, Kits are available on the Dark Web. Taking a shotgun approach, collect some email addresses and for a few dollars, you will find someone somewhere that will click something when they should have reported the attack. Pay more, and get more sophisticated attack capabilities
The platforms to be attacked are a relatively small number. This allows attackers an advantage to be able to specialize. If the attacker understands Exchange, Google or Yahoo email, the potential targets are in the millions.
Edge computing is already huge. No one knows the numbers but edge computing is an enabler for taking advantage of cloud services. The numbers are in the billions and the devices are ripe for specialization.
Awhile back, I read a comment by an IT manager, I am paraphrasing, “if I did not have end users, I would not have phishing attacks”. Attackers understand people and know how to collect personal information from social media. Plus one for the attackers and plus 0 for IT managers and end users.
Information Environment:
IT organizations have shown a tendency, when attacked, they don’t share information, and are in no hurry to notify users. Case in point – Uber. The corporation does what it thinks is correct in protecting itself, but the reality is that both the corporation and end users are more likely to be compromised multiple times. Lose – lose for everyone except the attacker.
Another down side to IT reticence, is that attackers have additional time to move from organization to organization.
There are tools available that IT managers can use to manage hardware and software risks. But tools available to measure probable human responses – the importance in understanding cognition – are far fewer than the hardware/software tools. Yet it is the inside user that is the soft target. Backwards.
Small to medium size businesses do not have the resources to predict and mitigate phishing attacks. Governments realize this by saying that it is the responsibility of small to medium size businesses to protect themselves. All the while, this is a global problem, but governments are not effective in protecting its citizens. Exactly the time when governments should be stepping in to protect those that elected government officials. Attacker 1. Small to medium size businesses 0.
Incentive Framework:
Phishing attackers have an integrated environment to share learning experiences, an open market to sell and buy tools, all thanks to the Dark Web. Corporations have a model of non disclosure, protect the stock price and give nothing to a competitor. The corporate environment and the Dark Web environment are opposites. The Dark Web proves itself over and over to be more efficient than the corporate world.
There are standards from NIST and ISO. Many corporations do not apply even the most basic standards and when corporations apply only the basics, hackers have learned how to compromise the partial implementation of standards. Case in point — password complexity and when to change passwords. Hackers figure out when the time is nearing for a change and attack. Users know it is time to change and are compromised. Hacker plus1. Corporations plus 0.
If you want a sure thing, bet on the phishing attacker. If you want to plug a huge attack surface, understand human cognition.
Thanks again to Arun Vishwanath for shining a light.
Discover more from Threat Detection
Subscribe to get the latest posts sent to your email.
